
Donavan Cheah gives us some of his thoughts on the subject of penetration testing, and his journey with the AWAE course in particu...
News and updates from OffSec

Donavan Cheah gives us some of his thoughts on the subject of penetration testing, and his journey with the AWAE course in particu...
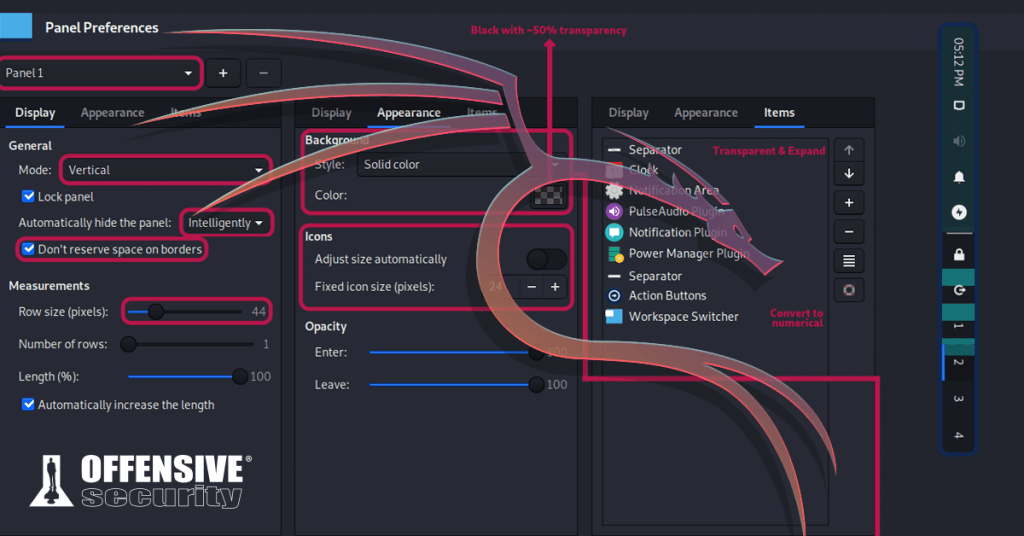
One of the designers on the Kali Linux team shares his top tips and tools to customize Kali Linux. Dig in under the hood with Dani...
OffSec student 0xklaue wrote this review of Advanced Web Attacks and Exploitation and the OSWE exam. Find out how to prepare and w...
With people located in over 24 countries, we've been working from our homes since our founding in 2006. Here's five tips on how to...

Find out where to start with OffSec's information security training courses. We outline our learning paths to certification and ca...
Get official answers to the most common questions about Penetration Testing with Kali Linux and the OSCP exam. Learn about require...

Penetration Testing with Kali Linux (PWK) has gotten a massive overhaul for 2020. Find out what’s new in Offensive Security's fo...
Learn how dedication, mindset, and community empowered Suhyun Smith in her OSCP certification journey, and get her tips for succes...

Meet Mihai, a 16 year old OSCP holder and PWK graduate out of Romania. Read more about his tremendous start and journey into infos...

OffSec student Christopher M Downs takes trying harder to another level: completing (and passing) his OSCP exam in the middle of a...

Our community manager, Tony Punturiero, breaks down the meaning of OffSec's legendary motto "Try Harder", and how it can help jump...

Samuel Whang, a PWK graduate, details his recommendations and a unique philosophical approach for those looking to pursue their OS...