Today we all constantly read about data breaches that could have been prevented if the impacted organization had just done what th...
News and updates from OffSec
Today we all constantly read about data breaches that could have been prevented if the impacted organization had just done what th...
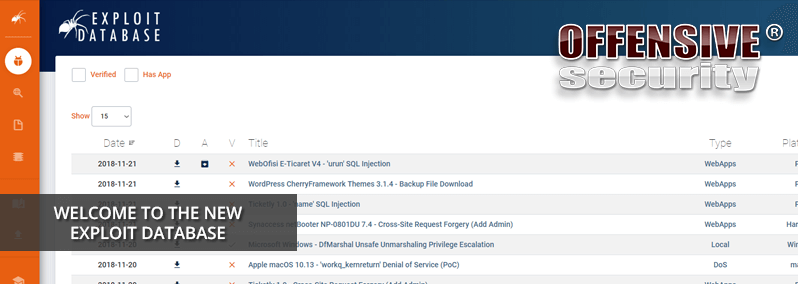
Offensive Security is delighted to announce the complete redesign of The Exploit Database (EDB), making it easier and faster than ...
It’s been a busy few months for us here, and for good reason. Today we are proud to announce our new partners at Offensive Secur...

When we started out with our online training courses over 12 years ago, we made hard choices about the nature of our courses and c...
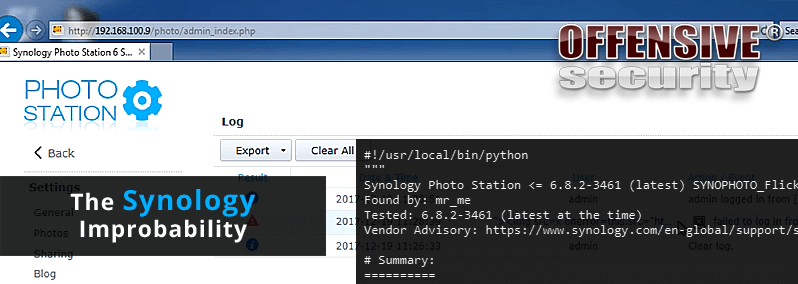
Recently, my manager purchased a Synology NAS device for me to do some backups. Since quite a few people I know use this particula...

Some time ago, we noticed some security researchers looking for critical vulnerabilities affecting "security" based products (such...
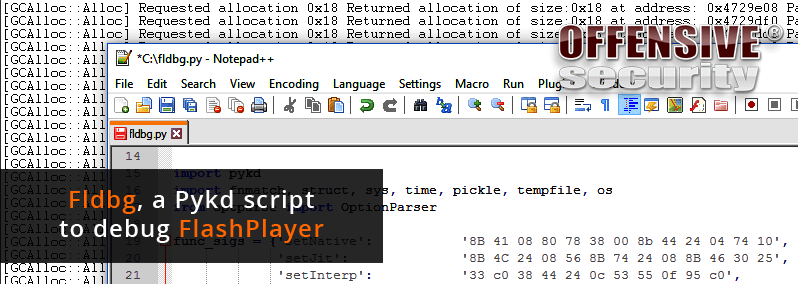
A few months ago, we decided to make a new module for our Advanced Windows Exploitation class. After evaluating a few options we c...

Admittedly, somewhat of a click-bait blog post title - but bear with us, it's for a good reason. Lots of work goes on behind the s...

Managing the Exploit Database is one of those ongoing tasks that ends up taking a significant amount of time and often, we don't t...
In our recent blog post "What it means to be an OSCP" we asked OSCPs to share their experience of what it means to have earned t...

The time has come for yet another Kali ARM image release with new and updated images. Our collection of supported ARM hardware gro...
A while back we introduced the idea of Kali Linux Customization by demonstrating the Kali Linux ISO of Doom. Our scenario covere...