OffSec's Csaba Fitzl shares how he reverse-engineered the macOS auto-login process, including the walls he hit, and the times he r...
News and updates from OffSec
OffSec's Csaba Fitzl shares how he reverse-engineered the macOS auto-login process, including the walls he hit, and the times he r...

In part one of this post, Tristram teaches you how to use TXT records to stage payloads that can be retrieved through DNS lookups.
Read about how the skillfulness of your security practitioners can impact your overall cybersecurity program and posture.

In this blog, we’ll briefly cover how CFI mitigations works, including CET, and how we can leverage COOP to effectively bypass I...

Join our OffSec bbq event for the chance to win some swag! Make your favorite bbq meal and share photos on Discord. Pic with the m...
Announcing changes to achieving OSCP Bonus Points and sunsetting of the PEN-200 legacy course exercises.
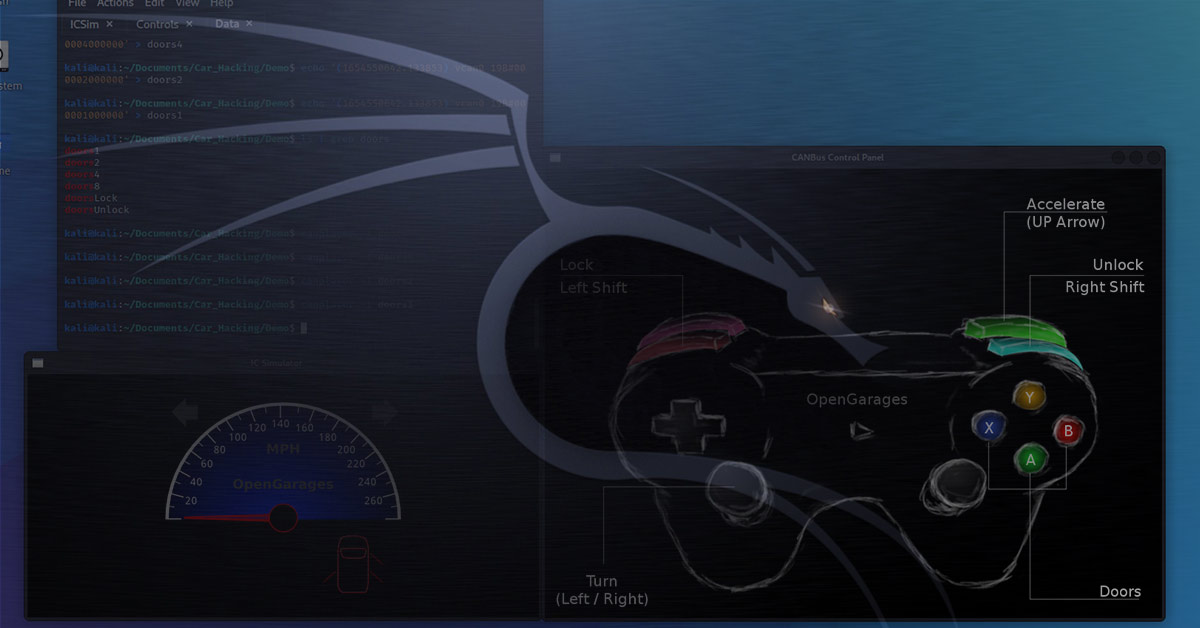
The CAN bus (Controller Area Network bus) is a central network that a vehicle communicates with its components. We can think of th...

Learn how to prepare your resume in an effective and professional manner to land a cybersecurity job.
Welcome to our Q2 update! This post discusses the launch of student discounts, OffSec Live, our Partner Program, and much more.
We previously explored how Cross-Site Scripting (XSS) makes for an excellent topic to understand the reach and impact of hacking...

We're excited to announce updates and new features to Learn Fundamentals that include new course Topics, badges and assessments, a...

TJ shows us how adversaries use macro weaponization techniques to abuse hidden functionalities contained in Office document proper...