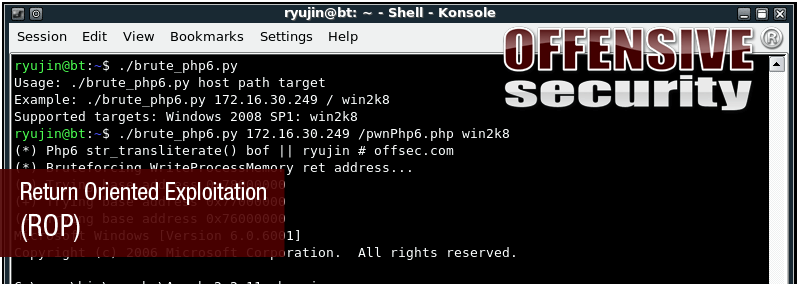
For all those who registered to AWE in BlackHat Vegas 2010 – we have special surprise for you… We’ve updated our “Bypassing NX” module with the buzzing ROP exploitation method.
Everything related to vulnerability and exploit development, including OffSec course updates and live training.
For all those who registered to AWE in BlackHat Vegas 2010 – we have special surprise for you… We’ve updated our “Bypassing NX” module with the buzzing ROP exploitation method.
Today (as promised in part 1 of the QuickZip Stack BOF exploit write-up), I will explain how to build the exploit for the quickzip vulnerability using a pop pop ret pointer from an OS dll. At the end of part 1, I challenged you, the Offensive Security Blog r
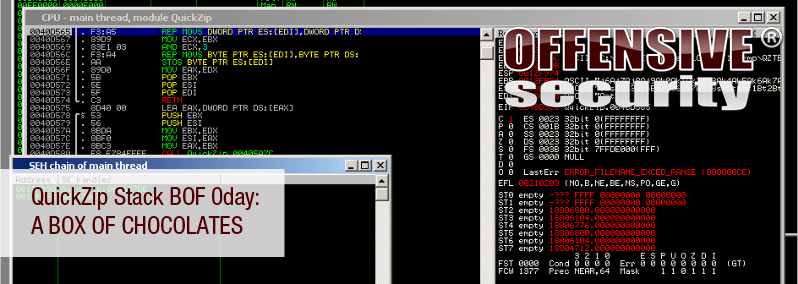
A few days ago, one of my friends (mr_me) pointed me to an application that appeared to be acting somewhat “buggy” while processing “specifically” crafted zip files. After playing with the zip file structure for a while (thanks again, mr_me, for docu
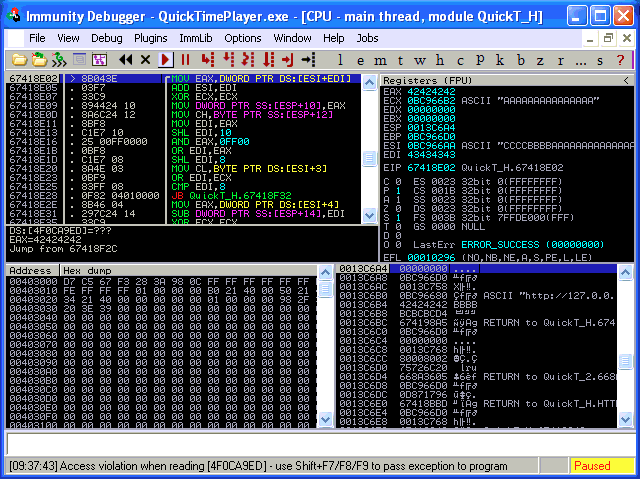
We recieved an interesting submission today at exploit-db from Dr_IDE. We have verified that both Quicktime and Itunes crash on Windows and OSX. The description reads: “There is a widespread failure in the way that (.MOV) files are handled by the Quickti
A remote Microsoft FTP server exploit was released today by Kingcope, and can be found at http://milw0rm.com/exploits/9541, https://www.exploit-db.com/exploits/9541/ A quick examination of the exploit showed some fancy manipulations in a highly restrictive en

Author: Matteo Memelli There goes our Information Security This is part 2 of our previous post about the Itunes exploit for windows. …little did we know that all the payloads being sent have to be pure AlphaNumeric (printable ASCII). The first thing to d

Author: Matteo Memelli When masochism just isn’t enough Our new AWE course is about to go live for the first time, in BlackHat Vegas. We chose the most interesting exploitation cases we’ve encountered, and dove really deep into them. We had many ex