Introduction
a11y.text IntroductionIf I had eight hours to chop down a tree, I’d spend the first six of them sharpening my axe. -Abraham Lincoln
Introduction to Metasploit | Metasploit Unleashed
This saying has followed us for many years, and is a constant reminder that approaching a problem with the right set of tools is critical for success. So what does this semi-philosophical opening have to do with the Metasploit Framework? Before approaching a penetration test or an audit, we always take care to “sharpen our tools” and update everything in Kali, especially the Metasploit Framework.
What is Metasploit?
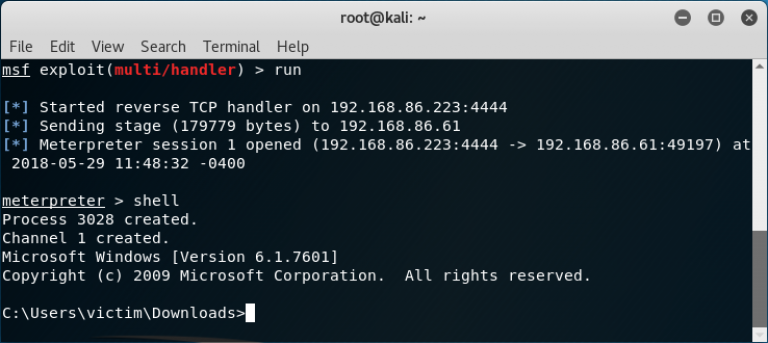
a11y.text What is Metasploit?The Metasploit Framework (MSF) is far more than just a collection of exploits–it is also a solid foundation that you can build upon and easily customize to meet your needs. This allows you to concentrate on your unique target environment and not have to reinvent the wheel. We consider the MSF to be one of the single most useful security auditing tools freely available to security professionals today. From a wide array of commercial grade exploits and an extensive exploit development environment, all the way to network information gathering tools and web vulnerability plugins, the Metasploit Framework provides a truly impressive work environment.
This course has been written in a manner to encompass not only the front end “user” aspects of the framework, but rather give you an introduction to the capabilities that Metasploit provides. We aim to give you an in-depth look into the many features of Metasploit and provide you with the skills and confidence to take advantage of this amazing tool.
I Don’t Understand Command XYZ, What Should I Do?
a11y.text I Don’t Understand Command XYZ, What Should I Do?In learning how to use Metasploit, a degree of prerequisite knowledge is expected and required of students before the content provided in this course will be useful. If you find you are unfamiliar with a certain topic, we recommend you spend time engaging in self research on the problem before attempting the module. There is nothing more satisfying than solving a problem yourself, so we highly encourage you to Try Harder™