Vulnerability Scanning
a11y.text Vulnerability ScanningVulnerability Scanning – db_nmap discovery example | Metasploit Unleashed
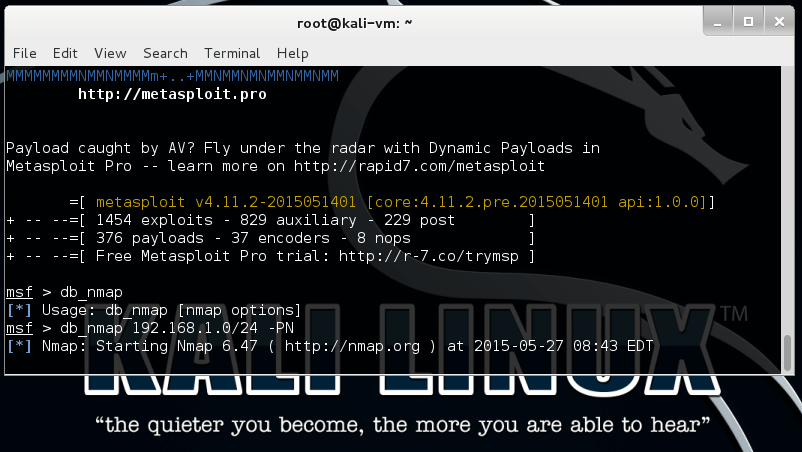
Discovery Through Vulnerability Scanning
a11y.text Discovery Through Vulnerability ScanningVulnerability scanning will allow you to quickly scan a target IP range looking for known vulnerabilities, giving a penetration tester a quick idea of what attacks might be worth conducting.
When used properly, this is a great asset to a pen tester, yet it is not without it’s draw backs. Vulnerability scanning is well known for a high false positive and false negative rate. This has to be kept in mind when working with any vulnerability scanning software.
Lets look through some of the vulnerability scanning capabilities that the Metasploit Framework can provide.