A couple of weeks ago, we had the opportunity to scan and map a large IP address space covering just over 3 million hosts. Our tool of choice for this was the fast and capable masscan, which is packaged in Kali. While masscan has several convenient output formats, such as binary and XML, one feature we were missing was an easy way to search our results. We quickly whipped up a little web interface that would allow us to import and search within a masscan XML output file. This feature proved very useful for us – as once we identified a specific vulnerable pattern on a machine, we could easily cross reference this pattern with the millions of discovered hosts in our database.
Setting up the MASSCAN Web Application
The setup of the masscan web user interface is pretty standard and straightforward. You will need to create a MySQL database, import the database schema, plop the PHP files under your web root, and edit the config file with the correct details. Here’s what this process would look like.
First, install and setup your web server and some other required packages, checkout a copy of the masscan-web-ui repository, and copy over the MASSCAN web ui files to the web root:
root@kali:~# systemctl start mysql
root@kali:~# systemctl start apache2
root@kali:~# git clone https://github.com/offensive-security/masscan-web-ui
root@kali:~# mv masscan-web-ui/* /var/www/html/
root@kali:~# cd /var/www/html/
Next, you’ll need to create a MySQL database and user for the web application and then import the masscan database schema.
Enter password:
Type 'help;' or '\h' for help. Type '\c' to clear the current input statement.
mysql> create database masscan;
Query OK, 1 row affected (0.01 sec)
mysql> CREATE USER 'masscan'@'localhost' IDENTIFIED BY 'changem3';
Query OK, 0 rows affected (0.00 sec)
mysql>GRANT ALL PRIVILEGES ON masscan.* TO 'masscan'@'localhost';
Query OK, 0 rows affected (0.01 sec)
mysql> exit
Bye
root@kali:/var/www/html# mysql -u root -p masscan < db-structure.sql
Enter password:
root@kali:/var/www/html# rm db-structure.sql README.md
Lastly, you need to update the web configuration file with the MySQL user and database information that you configured above.
define('DB_DRIVER', 'MySQL');
define('DB_HOST', 'localhost');
define('DB_USERNAME', 'masscan');
define('DB_PASSWORD', 'changem3');
define('DB_DATABASE', 'masscan');
With everything configured, you can now use masscan to scan your targets with the banner checking option, while specifying an XML output format for the results. More information about banner grabbing with masscan can be found on the masscan GitHub page.
Once all of the scans have been completed, it’s time to import the scan results. In this example, we imported the results of two class A scans, while choosing to clear the database when importing the first results file.
-rw-r--r-- 1 root root 212929324 Dec 1 13:23 scan-01.xml
-rw-r--r-- 1 root root 700816226 Dec 1 13:55 scan-02.xml
root@kali:/var/www/html# php import.php scan-01.xml
Do you want to clear the database before importing (yes/no)?: yes
Clearing the db
Reading file
Parsing file
Processing data (This may take some time depending on file size)
Summary:
Total records:738279
Inserted records:738279
Took about:3 minutes,18 seconds
root@kali:/var/www/html# php import.php scan-02.xml
Do you want to clear the database before importing (yes/no)?: no
Reading file
Parsing file
Processing data (This may take some time depending on file size)
Summary:
Total records:2411974
Inserted records:2411974
Took about:9 minutes,41 seconds
root@kali:/var/www/html#
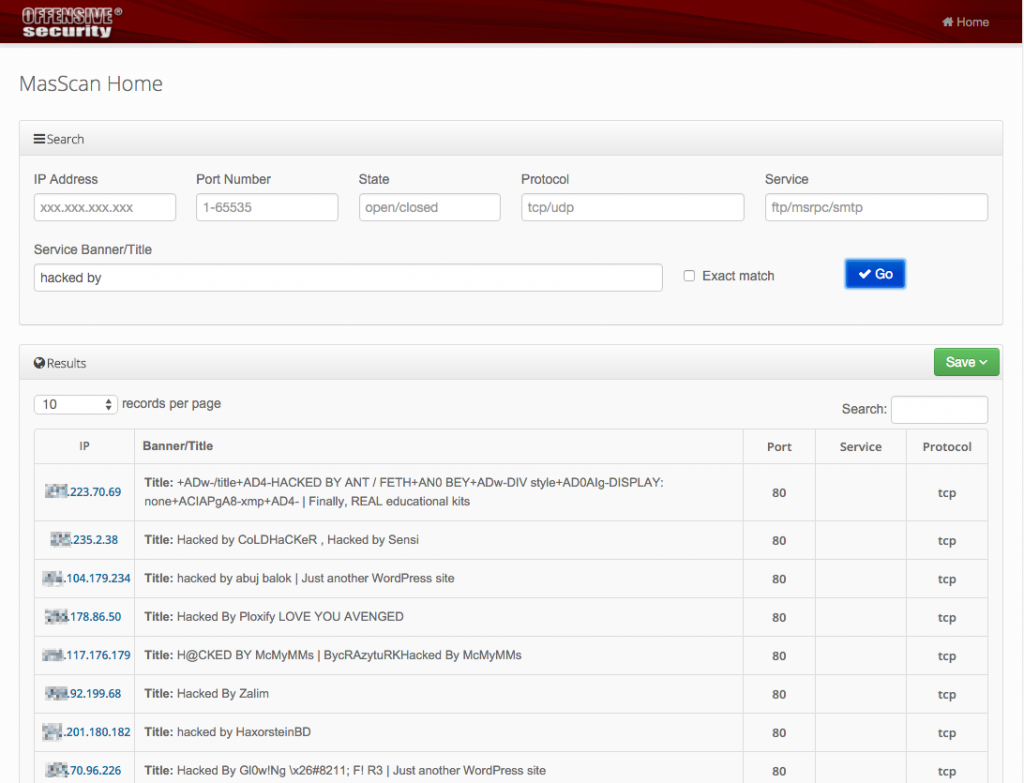
All that remains is to browse to the web application with a total of more than 3 million results now easily searchable.
For more information and to try out the masscan-web-ui for yourself, you can check out our GitHub project page.