Note: This is an article by Nullg0re and first appeared on January 11, 2021. Republished with permission from the author.
Evasion Techniques and Advanced Breaching
This blog post will cover some basics about the course and my thoughts, including:
- Quick Definition of a Red Team
- Pricing
- Syllabus
- Course Structure
- Meat and Potatoes of the course
- Course Challenges (“Try Harder”)
- OSEP Exam (Will updated once I have taken the exam)
- Takeaways/Recommendations
- Additional Studying Material
What is a Red Team?
A Red Team engagement is an exercise conducted by a Penetration Testing team and a client/customer’s Blue Team.
The idea of a Red Team Engagement is to test the security wherewithal of a given customers defensive teams. The analogy that I am most fond of is:
Red Team is adversary emulation. Blue Team’s sparring partner & coach in a way.
https://twitter.com/pmelson/status/1337210673604997122 – Paul Melson via Twitter
Red Teams are designed to keep a company’s defensive operations in proper fighting condition, so that when a real adversary steps into the ring, the company’s Blue Team knows what to do.
Disclaimer: This course is NOT a red team course.
This course is designed to teach Penetration Testers how to perform advanced Penetration Testing activities.
While many of the techniques and tooling could be utilized during a Red Team engagement, Offensive Security is not teaching this course from the perspective of “We will teach you how to Red Team.”
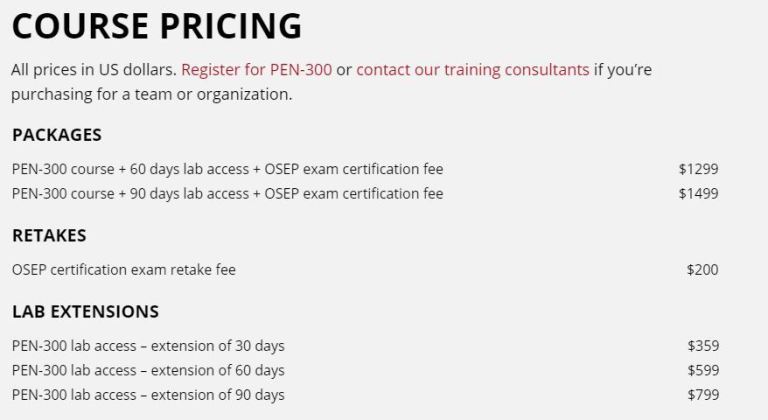
Pricing
Pricing as of January 11th, 2021 and subject to change – see https://www.offsec.com/pen300-osep/ for current prices.
While I cannot recommend any particular path for anyone because everyone learns differently, I can tell you the path that I took.
I chose the PEN-300 course with 90 days lab access. I intentionally chose the longer lab time, because of my family, work, and Bug Hunting responsibilities. I was able to complete the course work in about 3 to 4 weeks, and ran through the course challenges at least twice during that 90 window.
Syllabus
The course syllabus can be found here:
https://www.offsec.com/documentation/PEN300-Syllabus.pdf
Course Structure
When you sign up for the course, Offensive Security will send you a 704 page lab manual and a series of instructional videos. To get the most out of the course materials, I’d recommend watching both the videos and reading the manual.
While they cover the same material, sometimes the video does a better job explaining a certain topic than the manual, and other times the manual does a better job than the videos.
Get Ahead in Your Career with PEN-300
Meat and Potatoes
I’m going to intentionally take a high level approach.
Let me first state that the OSEP course does not teach MacOS exploitation at this time. It may in a future release but not as of Jan 11, 2021.
Right away, we jump into programming fundamentals with the “Operating System and Programming Theory” chapter. This chapter goes into some basics of programming concepts, the usage of Win32 APIs, and how they are going to be applied in the course.
This course does a very impressive and consistent job of starting with theory and then diving into practical application of that theory. Every single chapter follows the theme of “Let’s hit you with the theory, then let’s play around a bit in real time.”
In my opinion this is the best way to teach these kinds of concepts. I have taken some other “prominent” advanced penetration testing courses through other organizations, and I must say – hands down – Offensive Security knows how to throw down when it comes to training.
Next up, we get into “Client Side Code Execution With Office”. This chapter goes into how to get code execution through Microsoft’s Visual Basic For Applications (VBA – Word/Excel Macros) and starts us on the path of writing code for phishing.
I can tell you right now – this course does an amazing job at bridging the gaps between the original OSCE and OSEE. One of the techniques taught in the OSEE is to dynamically load DLL’s into a process using ROP gadgets.

OSEP teaches the same technique through the use of a programming language, making the concept easier to understand and allowing students to walk before they run.
Next up is “Client Side Code Execution with Windows Script Host”. This chapter adds onto the previous chapter and starts introducing public code repositories to assist in phishing.
Skipping ahead in the syllabus a bit, we land on “Antivirus Evasion”. Very cool techniques on evading antivirus are taught in this section, and we get our first introduction into WinDBG (something that is used heavily in OSEE).
Other Evasion Techniques that are taught in this course:
- Evading Application Whitelisting
- Finding new ways to bypass AMSI
- Bypassing various Antivirus Products
- Bypassing PowerShell’s Constrained Language Mode
- Bypassing Network Filters such as:
- Web Filtering
- DNS Filtering
- Usage of Domain Fronting
- Etc
What makes OSEP such an excellent advanced penetration testing course is that OSEP is one of the few Advanced Penetration Testing courses I’ve taken where Linux penetration testing techniques are taught as well.
Some of the Linux techniques taught are:
- Using VIM as a backdoor and keylogger
- Bypassing Linux Antivirus Solutions
- Shared Library Hijacking
The course also offers a deep dive into Kiosk enumeration, breakouts, escalation, and more.
Additionally, there are a LOT of opportunities to write custom code. While Antivirus solutions might quickly recognize Mimikatz, you have the opportunity to write custom code to perform Mimikatz-like activities and completely bypass Antivirus.
Offensive Security completes the course with MSSQL and Active Directory attacks that should be in every advanced penetration testing course offered.
These attack techniques include:
- Exploiting Linked Databases
- Unconstrained Delegation Attacks
- Resource-Based Constrained Delegation Attacks
- Taking over a domain
- Taking over a forest
- Taking over additional forests
This course teaches students from Initial Entry all the way to taking over the Forest, step by step.
All in all, excellent course OffSec!
Challenges
In true Offensive Security fashion, there is always an opportunity to “Try Harder”. For OSEP, this opportunity takes the form of lab Challenges.
These 6 challenges are extremely well written and are designed to test everything you’ve learned in the course, as well as test your “Try Harder” chops.
These challenges touch every aspect of what is taught in the course.
They are small, multi-machine lab environments that force the student to do everything from landing the initial shell, to pivoting into the network and moving laterally from machine to machine until you’ve become DA.
Some of these challenge labs even include multi-domain setups, where you have to compromise Domain A in order to move laterally into Domain B and take it over as well.
Each machine has a “local.txt” and a “proof.txt” to show you have landed the initial shell and have escalated privileges on the machine.
Lastly, these challenge labs include both Linux and Windows machines, so it really is a good representation of what is taught in the course.
OSEP Exam
I have not yet taken the exam. I am scheduled to take the exam on February 9th. I will update the blog with my attempt afterwards.
Takeaway / Recommendation
I thoroughly enjoyed this course. Not only did I improve my own skills, but I had a lot of fun doing it. I can take the skills taught in this course and immediately apply it to my day job.
I would recommend this course to any Penetration Tester who is looking to improve their own skills and any Blue Team operator, simply to have a better understanding of these types of attacks and to better prepare you to take on adversaries.
Additional Studying Material
Before I started the course, I made a GitHub repository that contains a large list of topics covered in the exam. Feel free to check out my unofficial supplemental learning material:
https://github.com/nullg0re/Experienced-Pentester-OSEP
Anthony Larcher-Gore (aka nullg0re) is a United States Marine Corps veteran, penetration tester, and bug bounty hunter. He also teaches cybersecurity courses at a local community college as an adjunct professor. Anthony holds a dozen infosec certifications, including the OSCP, OSWP, OSWE, OSCE, and OSEE. He lives with his wife, children, and dogs outside of the Chicagoland area. Connect with Anthony on his website.