Discord Server Updates
Server Statistics
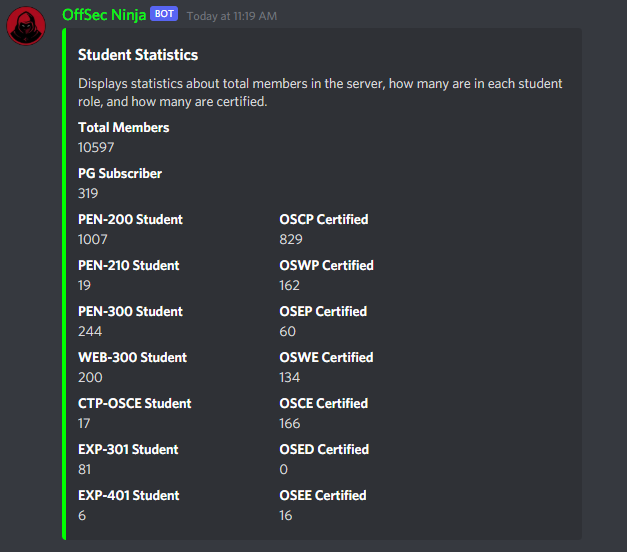
It’s been nearly a month since we’ve migrated the community from our Rocket.chat self-hosted platform to Discord.
Before Rocket.chat closed, we had roughly 8200 users with 200 concurrent online users at any point in time. Since we’ve migrated to Discord, we have already surpassed those numbers in just a month. As of the end of May , there are 10,597 registered users, with an average of 2800 online concurrent users. Both numbers are growing daily!
All of us at OffSec couldn’t be happier with how well the community continues to shape and grow as the days pass.
We’re going to be doing a giveaway in the near future for the community. This is something we want to do as a way for us to give back to all of you for being amazing! Please stay tuned to our social media and Discord announcements channel.
Role Verification
We launched Discord with the validation of student status and certifications acquired as a manual process. The only automated process we had in place was to validate your Proving Grounds Practice subscription.
To create a better user experience, we’re in the process of expanding our automated validation process to student and certified roles. This will remove the validation wait time on both ends for students
Once you’ve acquired a certification, you can automatically get your nifty Certified role, related to whichever course you recently passed!
Support Model Updates
As some of you may have noticed we are now allowing motivated community members to step in and assist with student questions. We want the community to be more inclusive in helping support each other with our courses and Proving Grounds platform.
For those who have validated their student status, certifications acquired, or seeked mentorship from our Student Admins, you may recall being invited to a private 1:1 chat room. Previously, these rooms were not being logged. Anything being discussed wasn’t recorded and there wasn’t a way for us to send you a copy of the discussion if you requested it. Additionally, there wasn’t a way for us to analyze how helpful we were in terms of providing mentorship. Moving forward all rooms will be logged. A notification will be displayed in the first channel message from our bot, OffSec Ninja.
Why the sudden change? Other than the aforementioned reasons, we would like to align our services with what was previously offered on Rocket.chat, and the support system before Rocket.Chat.
Community Events
Our community management team is in the process of developing events for the community to partake in.
Outside of weekly office hours held by Tjnull and FalconSpy, the events range from game nights playing against our staff and fellow community members, Dungeon & Dragon sessions, and Vulnhub walkthroughs, to just hanging out in voice chat getting to know one another better. If you have ideas or something you would like to see, let us know on Discord or community [at] offensive-security [dot] com.
You may view the calendar via our Events page and click on Community Events. You may find it helpful to use a service that converts the event to your local date and time to know when the event is taking place.

OffSec Podcast
Episode 2 with BlindHacker – Supporting others with Disabilities
For the second episode of the official Offensive Security Podcast, Tjnull and Jeremy (Harbinger) sat down with a member of the community known as BlindHacker.
They discussed the challenges and opportunities around improving accessibility for the disabled community within the infosec field. BlindHacker provided insights and perspective on how we can all help to provide more accessibility options, considerations and accommodations to people across a range of disabilities — and why it’s critical for filling the skills gap in cybersecurity going forward.
You can learn more about BlindHacker on Episode 2 via https://www.offsec.com/podcast/
Episode 3 with dade – Hacking and making music
Tjnull and FalconSpy sat down with dade, an experienced Red Teamer and music artist about his experiences in the field.
They discussed the importance of note taking and communication skills in InfoSec, the most important qualities of being a pentester or red teamer, and dade’s project known as Natlas – what it is and what it does. In addition, dade provided advice for those who want to develop and release their own tools for the community. Last but not least: how dade wound up writing and recording the hip-hop/rap song, “Red Team”
You can learn more about dade on Episode 3 via https://www.offsec.com/podcast/
Episode 4 with S1REN
Tjnull and Harbinger talk infosec with S1REN, a very accomplished member of the community and a moderator of OffSec’s Discord. Among other things, they discussed how S1REN got into infosec and why, some advice for women looking to get into infosec, and why BASH, Python, and TCP/IP are so essential for people to get into before getting into security. They also touched on good ways to break into infosec and some things S1REN would like to see changed in the infosec field.
You can learn more about S1REN on Episode 4 via https://www.offsec.com/podcast/
Community Projects
We asked the community to provide us with any nifty applications, tools, images, videos, etc they have created. Below are May’s spotlight projects:
rootend – Enumeration & Priv Esc Tool
Developed by twelvesec, rootend is is a python *nix Enumerator & Auto Privilege Escalation tool.
ssj – our everyday Linux distribution gone Super Saiyan.
Developed by (https://twitter.com/secguy), ssj is a tool just like Kali KeX, and is no different from WSL2 + VNC. secguy realized there is no way someone without knowing how docker works can use kali in docker. So he built an image with kali-linux-large metapackage and created a silly script to create a .desktop application launcher that would fire up a terminator window from within the docker image on any host Linux distribution. This way anyone can have access to the toolkit without the overhead of a virtual machine and knowledge of docker. The only stepsecguy took was to automate the complete setup of the docker image. The Dockerfile for the docker image is public at https://github.com/scarfaced18/docker-images/blob/main/ssj/Dockerfile. It is just an immutable version of Kali Kex for GNU/Linux distributions with docker installed.
Autorecon – multi-threaded network reconnaissance tool
Developed by Tib3rius, autorecon is a multi-threaded network reconnaissance tool which performs automated enumeration of services.
That’s All For Now Folks
Stay tuned to future blog posts and our social media platforms for anything new we release.
We intend to release more podcasts, Ask Me Anything events, and even have some upcoming webinar events.
