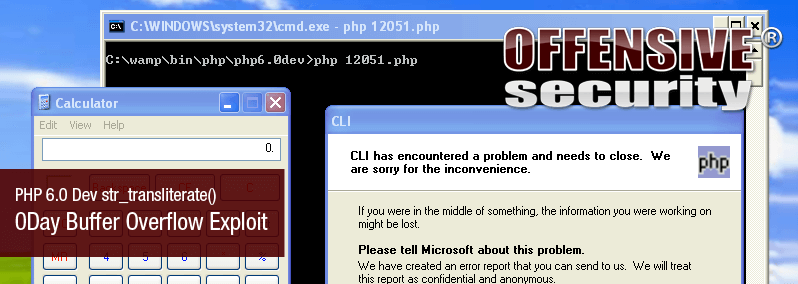
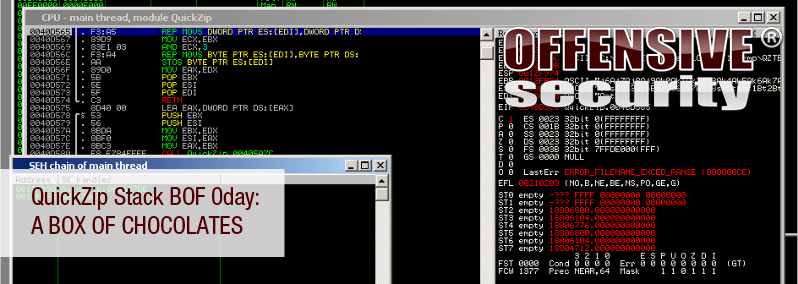
In a recent engagement, we had the opportunity to audit a leading Antivirus Endpoint Protection solution, where we found a multitude of vulnerabilities. Some of these made it to CERT, while others have been scheduled for review during our upcoming AWE course a