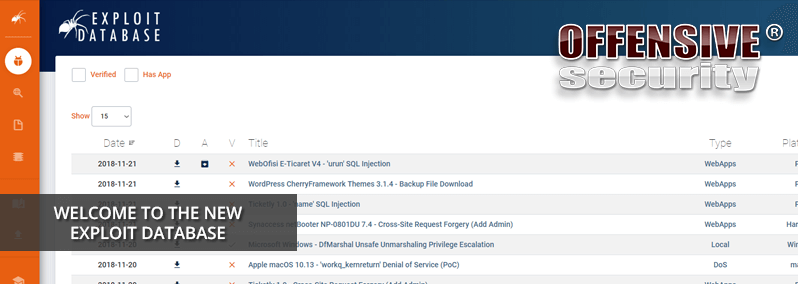
Offensive Security is delighted to announce the complete redesign of The Exploit Database (EDB), making it easier and faster than ever to find the data you need and presenting it to you in a responsive dashboard layout.
Offensive Security is delighted to announce the complete redesign of The Exploit Database (EDB), making it easier and faster than ever to find the data you need and presenting it to you in a responsive dashboard layout.

Managing the Exploit Database is one of those ongoing tasks that ends up taking a significant amount of time and often, we don't take the time to step back and look at the trends as they occur over time. Have there been more exploits over the years? Perhaps fe
New Features in the Exploit Database Over the past 6 years, we have been maintaining and updating the Exploit Database on a daily basis, which now boasts over 35,000 exploits. While we constantly work on improving our back-end and entry quality. Over the years

We have recently completed some renovations on the Exploit Database backend systems and moved the EDB exploit repository to Github. This means that it's now easier than ever to copy, clone or fork the whole repository. The previous SVN CVS has been retired.
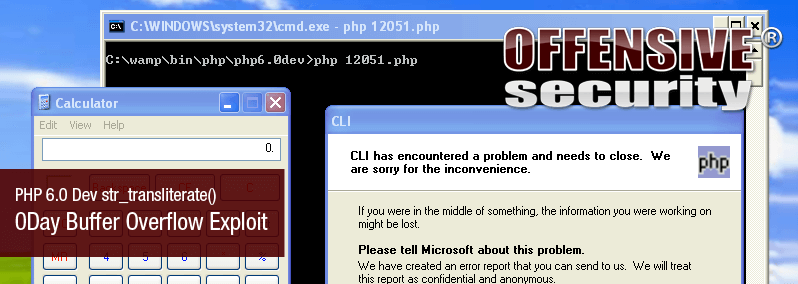
An interesting submission to EDB today from the guys at http://www.nullbyte.org.il - a PHP 6.0 0day buffer overflow.
After a short and intense setup, we are ready to present the Offsec Exploit Archive. We’ve recreated the milw0rm database, updated it and are now accepting submissions. The purpose of the site is to provide researchers and security enthusiasts a reposito