
Learn how social engineering exploits human vulnerabilities through manipulation and deception. This guide covers different tactics cybercriminals use and key strategies to protect your organization.

Learn how social engineering exploits human vulnerabilities through manipulation and deception. This guide covers different tactics cybercriminals use and key strategies to protect your organization.
It’s hard to believe that the social-engineer.org project began 14 months ago. This project started from a simple idea to build the world’s first framework for social engineers. In these 14 months, this project has grown into the leading resou
Are you looking for a real Social Engineering CTF challenge? Join Social-Engineer.Org and Offensive Security in the Official Social Engineering CTF hosted at Defcon 18.
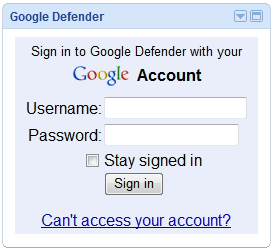
A new report by emgent shows malicious Google Gadgets in action. The vulnerability lies in the ability of a malicious user to add their own Gadgets on a separate domain space, without Google's authorization. The attack variant shown in the movie can be altered